Is a Continuous Process Designed to Keep All Personnel Vigilant
Shifting organizational behavior requires a recognition that simply exposing employees to security-related information will never be enough. Instead, it is imperative to train secure reflexes through intentional and methodical simulated testing so that employees are continually exposed to the situations in which you hope they will exhibit secure behavior. Some security and organizational leaders might be hesitant to phish their users, fearing that end-users or managers could react negatively to the experience. In fact, some organizations may even have horror stories of phishing simulations that have backfired, resulting in more harm than good. Yet, security leaders, auditors, and adult-learning experts agree that the best way to train secure reflexes is through simulation (not information). It is possible to work through concerns related to simulated phishing and, in fact, make the experience positive for end-users and management alike. Use the following five principles to build a positive anti-phishing behavior management program: Creating your anti-phishing behavior management program according to these five principles will ensure that your program is seen as something that builds-up employees rather than tearing them down. These principles are aimed at recognizing that humans can become an effective last line of defense for your organization when given proper training, motivation, and support. Follow these guidelines to ensure the success of your program. Need help getting started? KnowBe4's Automated Security Awareness Program takes away all the guesswork. Answer 15-25 questions about your goals and organization and get your customized program in just 10 minutes! * This list is also available as aninfographicAvoid Potential Pitfalls in Phishing Your Users
Five Principles to build positive anti-phishing behavior management programs

Avoid these top 10 security awareness training program fails
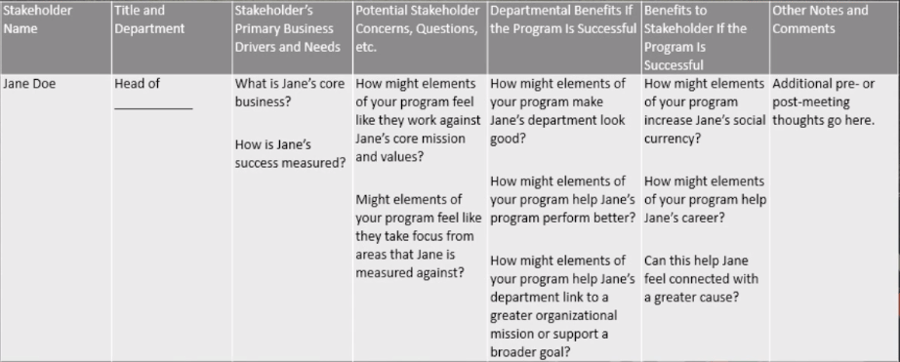
With so many regulations and audit standards requiring organizations to provide critical security-related information and training programs for their employees, it can be shocking that security leaders often encounter high-level "push back" when seeking to implement security awareness and training programs. To overcome this situation, propose your program in a way that addresses executive concerns, links to corporate objectives, and tells a story. This is accomplished in three steps: Habit five of Stephen Covey's "Seven Habits of Highly Effective People" states, "Seek first to understand, then to be understood." Dr. Covey writes, "If you're like most people, you probably seek first to be understood; you want to get your point across. And in doing so, you may ignore the other person completely, pretend that you're listening, selectively hear only certain parts of the conversation or attentively focus on only the words being said, but miss the meaning entirely. So why does this happen? Because most people listen with the intent to reply, not to understand. You listen to yourself as you prepare in your mind what you are going to say, the questions you are going to ask, etc. You filter everything you hear through your life experiences, your frame of reference. You check what you hear against your autobiography and see how it measures up. And consequently, you decide prematurely what the other person means before he/she finishes communicating." It is vital to recognize that most business leaders (and end users) simply will not care about security in the same way that a security professional does. People don't care about security for the sake of security alone. What they care about is the result that a sound security strategy can provide and the impacts/risks associated with the lack of a sound security strategy. Use this understanding to inform the methods that you use to engage the organization and business leaders. When reporting your security awareness successes, continue to remind the executive team why the program is important, and how the activities and metrics connect with the motivations outlined in points 1 and 2, above. In the end, many of the metrics can be the same as you would normally report (for example, course completion rates, phishing test outcomes, and so on), but the difference here is that you are able to put these numbers into context. This context is used to tell the story of how your security awareness and training program is strengthening the overall security culture of the organization, thereby reducing risk, potentially increasing productivity, and having a positive impact on the organization's ability to execute. "Culture eats strategy for breakfast." - Peter Drucker, Management Consultant, Educator and Author Communication Strategy is Key Any time you are presenting data numbers, don't leave the interpretation up for chance. The 'what' is the data, with every 'what' comes a so what? meaning what does that data actually mean? and a now what?, or what do we do in light of that information? Any time you have a what, you need to answer the so what and the now what, otherwise you're leaving one or both of those things up for interpretation and that's a chance you cannot afford to take. Your communication strategy throughout the whole process is key. You want to tell a memorable story, the moral being you need security awareness training. Use statistics and charts and graphs to support that story. Capturing Executive Attention What's in it for them - Answer the "so what" question. Answer specifically for each member of the executive team what is going to matter most for them with the output of a security awareness training program. This can be talked about positively - increased resiliency that leads to stabilization of environment, higher employee productivity or negatively - pain that can be avoided when this is done right (data doesn't get exposed, users don't get compromised, etc.). Outline clear connections - Showing connection between the action of training and things that are important for that executive. Could be a specific system, business outcome, specific project, a regulation they are accountable for. Measurement and stories - Talk about what is going to be measured, how it will be presented, and use that to get into the morality (this is what goes wrong without a security awareness program, here is what can go right, etc.) Be on the Lookout for Ways To: Use SMARTER Goals Show that you are being very intentional about starting your program and you will more likely get the support, budget and resources you need to get it started. Use a SMARTER goal-setting framework, goals should be Specific, Measurable, Actionable, Risky, Time-keyed, Exciting and Relevant. Goals like "The goal is to reduce our phish-prone percentage" or "To be able to engage employees so they are more aware of the risks and threats around them" are not specific or measurable and are certainly not exciting. An example of a SMARTER goal would be: We are going to reduce our phish-prone percentage from an initial baseline of 30% down to 15% within the next 45 days. You will know for sure whether you've hit the goal or not once that 45 days is up. With this framework in mind, it is much easier to build out your training plan and reporting schedule around these types of goals. Brainstorming Worksheet for Gaining Support We recommend filling something like the below sheet out for each executive you need to get buy-in from. This isn't to share with anyone, it's a tool for you to help before you start meeting with your executive team. Find ways to amplify their value proposition and address or minimize their concerns early on. Try to have one-on-one conversations before you officially ask for support so there are no major surprises when that time comes. It's a Marathon, not a Sprint It's very important that you present this as an ongoing program from the very beginning - not a one and done. Think about the difference between an event and an ongoing effort… and the difference between a sprint and a marathon. Time and consistency make a BIG impact in changing behavior for the better.How to Gain and Maintain Executive Support for Your Security Awareness Program
How to work through "push back" when seeking to implement security awareness and training programs

So, what motivates a business leader? The answer is: business risks and business outcomes. Therefore, it is helpful to position your security awareness and training program in this context. To do this, consider highlighting the following:
Where possible, you need to speak the language of "the business" and report in a way that shows relevance to organizational outcomes. Notice that this is directly related to the other points mentioned in this article. In order to report in a relevant way, you first need to understand your organization's targets and the agreed-upon risks.Maintaining Executive Support for Your Program
Source: https://www.knowbe4.com/security-awareness-training
0 Response to "Is a Continuous Process Designed to Keep All Personnel Vigilant"
Post a Comment